Table of Contents
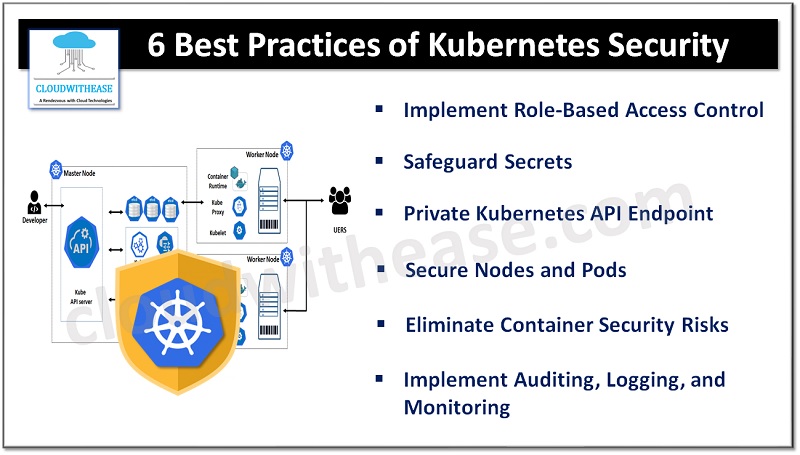
Kubernetes has become the go-to container orchestration platform for organizations of all sizes. Its ability to manage and scale containerized applications has revolutionized the world of software development. However, with the increased adoption of Kubernetes comes the need for robust Kubernetes security practices to protect your cluster from potential threats.
In this article, we will explore the best practices for securing your Kubernetes cluster, ensuring that your applications and data are safe from unauthorized access.
1. Implement Role-Based Access Control (RBAC)
Role-Based Access Control (RBAC) is a critical security feature in Kubernetes that allows you to control who can access the Kubernetes API and what actions they can perform. By enabling RBAC, you can limit users and groups to only the necessary permissions required for their tasks, following the principle of least privilege. This ensures that each user and Kubernetes service account has the minimal set of privileges needed, reducing the risk of unauthorized access.
To implement RBAC, you should enable it in your Kubernetes cluster and carefully manage the authorization policies. Avoid granting cluster-wide permissions and restrict the use of cluster admin privileges to only those who truly require them. Cloud service providers often offer identity and access management services that can further enhance RBAC capabilities. Additionally, consider using multifactor authentication (MFA) to strengthen authentication to the Kubernetes API.
2. Safeguard Secrets to Ensure Kubernetes security
Kubernetes secrets store sensitive data such as passwords, tokens, and SSH keys. It is crucial to treat secrets with utmost care and ensure they remain confidential. To enhance security, follow these best practices:
- Encrypt secret resources in etcd: Encryption at rest ensures that even if an attacker gains access to etcd backups, they cannot view the content of secrets.
- Protect communication channels: Secure the communication between users and the API server, as well as between the API server and kubelets, using SSL/TLS encryption.
- Implement short secret lifetimes: Set short lifetimes for secrets and automate their rotation to make it harder for attackers to exploit them.
- Review third-party integrations: Carefully assess RBAC permissions and access requested by third-party integrations to prevent compromising the security of your cluster.
3. Opt for a Private Kubernetes API Endpoint
Configuring the Kubernetes API endpoint as a private endpoint can significantly enhance the security of your cluster. In a private cluster, the API server within the control plane has a private IP address, making it inaccessible from the public internet. By utilizing private worker nodes and a private API endpoint, you can create fully isolated clusters that do not expose any public IPs or allow ingress/egress of traffic from the public internet. This level of network isolation ensures that your cluster remains protected from external threats.
Cloud service providers like Oracle Kubernetes Engine offer the flexibility to configure both the Kubernetes API endpoint and worker nodes, allowing you to create private clusters with ease. By controlling network access to the cluster API endpoint using security access control lists or network security settings, you can further strengthen the security of your cluster.
4. Secure Nodes and Pods
Nodes and pods are the building blocks of your Kubernetes cluster, and securing them is essential to maintaining a robust security posture. Consider the following practices:
Nodes:
- Harden the operating system: Ensure that the OS running on your nodes is hardened and regularly updated with security patches. Cloud providers often offer hardened OS images that you can use for your nodes.
- Limit network access: Configure your nodes to be on a private network, inaccessible from the internet. Use network access lists to control network port access and limit SSH access to the nodes.
- Follow security benchmarks: Adhere to security benchmarks such as the Center for Internet Security (CIS) Kubernetes benchmark to ensure that your nodes meet industry best practices.
Pods:
- Define network policies: Use network policies to restrict communication between pods within your cluster. Implementing network policies requires a network plugin that supports policies.
- Leverage pod security context: Utilize pod security context to define privilege and access-control settings for your pods. This allows you to specify the runtime execution properties of pods, such as running containers as privileged containers or accessing the host file system.
- Control pod assignment: Employ policies to control the placement of pods onto nodes, ensuring that pods are assigned to trusted nodes. Taint-based pod placement and eviction can be used to further restrict pod assignment.
5. Eliminate Container Security Risks
Containers play a vital role in Kubernetes, and securing them is crucial to maintaining the overall security of your cluster. Here are some best practices to eliminate container security risks:
- Secure container images: Implement security practices throughout the entire container lifecycle, from building and storing images to deploying them. Use hardened slim OS images and regularly update them with security patches.
- Scan for vulnerabilities: Utilize container image scanning tools to identify security vulnerabilities in your container images. Consider automating vulnerability scanning of third-party libraries used in your applications.
- Leverage container registry security: Use private container registries with proper access control and governance policies. Consider solutions that offer container image scanning, signing, and verification capabilities.
- Follow least-privilege principles: Ensure that the users running your applications within containers have the least level of OS privileges necessary for their processes.
6. Implement Auditing, Logging, and Monitoring
Auditing, logging, and monitoring are essential components of a robust security strategy. By implementing these practices, you can detect and respond to security incidents effectively. Consider the following steps:
- Enable audit logging: Enable and configure audit logging in your Kubernetes cluster to capture detailed information about API server calls. Save audit logs in a secure repository for analysis and compliance purposes.
- Establish cluster-based logging: Implement a centralized logging subsystem to record container activity within your cluster. Use tools like Fluentd to ingest container logs into a central logging platform such as Elasticsearch, allowing for easy analysis and monitoring.
- Monitor cluster components: Utilize monitoring tools like Prometheus, Grafana, or Jaeger to monitor the health and performance of your cluster components. Monitor containers, pods, applications, and services for any unusual activity or anomalies.
In conclusion, securing your Kubernetes cluster involves implementing a combination of best practices, covering various aspects such as access control, secrets management, network isolation, node and pod security, container security, and monitoring. By following these best practices, you can ensure that your Kubernetes cluster remains resilient against potential security threats. Stay vigilant, stay updated, and continuously reassess your security measures to protect your valuable applications and data.
Remember, the security landscape is ever-evolving, and it is essential to stay informed about the latest security practices and recommendations for Kubernetes. By adopting a proactive approach to security, you can mitigate risks and safeguard your cluster effectively.
