Table of Contents
Gone are the days of traditional approach to infrastructure deployments, application developments and security. This is further accelerated during the Covid-19 pandemic when enterprises were forced to build an application cloud modernization strategy overnight and make cloud security management among top priorities. It become imperative to weave security into every stage of application development to build and highly scalable application while meeting regulatory compliance requirements
Today we look more in detail about DevSecOps model and how it fits into the overall scheme of cloud security, how DevSecOps works, its advantages and use cases.
What is DevSecOps?
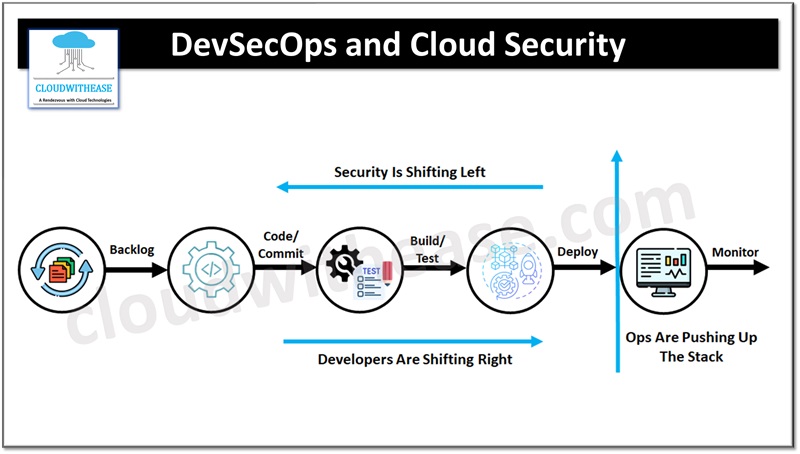
‘DevSecOps’ is gathering hype in the area of software development to secure an application and it is an extension of DevOps with security embedded in as ‘Sec’’. DevSecOps essentially focuses on integration of security from the initial stage of Software Development Life Cycle (SDLC) also known as ‘Shifting Security to Left or Left Shift security’ unlike conventional models where security checks and testing happens in later stages of SDLC.
Integration of security at the end of SDLC is not only expensive but also tricky to implement hence DevSecOps is an economical approach to safeguard software from security issues which would later become source of reckless cyberattacks. It lets developers perform regulated testing from the beginning, making application reliable and conductive to regular monitoring of operational vulnerabilities of software/ application.
DevSecOps in Cloud
DevSecOps is integration of continuous security principles, processes and technology into DevOps culture , workflows, and practices. It had brought together silos of development, infrastructure, operations, and information security into secure software development practice. DevSecOps also establishes accountability on every IT team member, making everyone from developer to engineer – owner of security. DevSecOps focus is on developing applications at an accelerated rate considering integration of security into DevOps every stage.
With DevSecOps businesses can:
- Reduce wastage, efforts, and resources to fix security issues
- Innovation is speed up and shorter time to market because of automation of security
- Automated incident reports, quicker and easier to detect and fix issues
- Implementation of preventive security controls on cloud
- Making security collective responsibility of all teams
- Easier to adopt zero trust security approach
- Designing applications with security built-in
- Automation of quality checks, testing and reporting
- Reduction in bottlenecks in Software development life cycle (SDLC)
4 Stages of DevSecOps Pipeline
A DevSecOps pipeline comprises four stages. Let’s look at each of the stages in more detail.
Building Stage
In this stage, static scanning of source code or Static Application Security Testing (SAST) is integrated which lets developers identify vulnerabilities and issues related to source code and send the feedback back to developers to resolve issues such as back door, poor source code issues etc. This helps to prevent passing vulnerabilities to the production stage.
Testing Stage
This stage is very critical in software development. Dynamic application testing (DAST) is integrated to imitate or simulate malicious attack from outside. The feedback enlists the possible ways in which an attacker can breach the software. These issues need to be addressed before actual deployment of software framework to protect from cyber threats.
Infrastructure & Compliance Analysis Stage
Scan focuses on configuration settings and system infrastructure. The compliance scan analyses system conformity to specific regulations such as HIPAA and HITRTUST controls.
Deploy or Release Stage
In this stage application is integrated with web application firewall (WAF) to prevent application to be subjected to cross-site scripting (XSS), cross site forgery, file inclusion, SQL injection, DDOS attack which could result in cyber incident
Nowadays, developers are using a variety of tools such as Gitlab, Jenkins, Jira, and Docker to have a cohesive environment for software development and release high quality products in a shorter time. Automation of the entire software development environment requires source control repositories, container registries, API management, configuration and hardware and software systems coordination, and overall monitoring to reduce human intervention.
