Table of Contents
A large number of businesses across the world are using cloud computing in one way or another. When utilizing the cloud, it is important to make sure that the organization has a secure cloud strategy that can guard against the major security issues associated with the cloud.
Enterprises that take advantage of cloud computing without being mindful of the potential security issues may be exposing themselves to a lot of financial and technological risks. Let’s discuss the key cloud vulnerabilities that come with using cloud technologies and measures to reduce them.
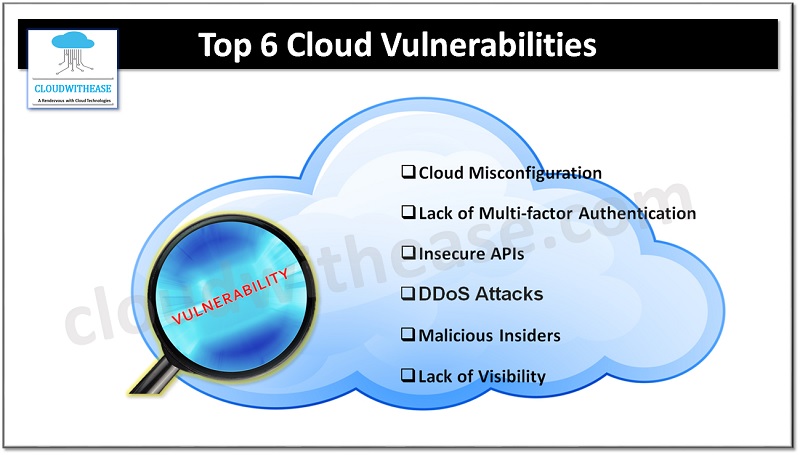
List of Cloud Vulnerabilities
Below is the list of common cloud vulnerabilities:
1. Cloud Misconfiguration
Approximately 75% of all organizations using cloud computing services have encountered misconfigurations that have an impact on the security of their systems. Common issues include usage of the default passwords, inadequate access limitations, mistakes in the administration of authorization controls, inactive data encryption, and more. The majority of these security flaws arise due to insider threats and a lack of security consciousness.
Inconsistent identity and access control (IAM) is a frequent vulnerability present in cloud computing systems.
According to a recent NSA study, cloud misconfiguration is one of the most frequent security risks encountered by companies.
Preventive Measures
- It is not advisable to assume that cloud configurations will stay the same indefinitely. Regular auditing and observation can assist in detecting any signs of incorrect settings.
- It is recommended to employ third-party tools to recognize any incorrect configurations of IAM policies, and a cloud-native application protection platform (CNAPP) can bolster the discernibility of a misconfiguration.
- It’s important to select the correct security measures that can provide a comprehensive collection of features, such as security administration, uncovering of potential threats, and avoidance of unauthorized access.
2. Lack of Multi-factor Authentication
Multi-factor authentication (MFA) is a process that requires a user to provide two or more pieces of evidence in order to access their account or data. As an example, a common MFA is when a person has to enter a username and password and then be asked to supply an additional validation such as a one-time code sent through SMS, email or a push notification on their mobile device.
Both passwords and identities of users are susceptible to theft, which makes the absence of multi-factor authentication a possible major security flaw.
Preventive Measures
- Introduce Multi-Factor Authentication (MFA) within your company to take advantage of the additional authentication process necessary to gain access to systems (like through a physical telephone or email address).
- It is mandatory to utilize multifactor authentication for any personnel who are given access to their accounts and details in the cloud.
3. Insecure APIs
The implementation of APIs can bring many advantages to companies, but it can be a major difficulty for their security teams. Even though APIs are intended to make cloud computing simpler, they are not always straightforward. There is a grey zone where APIs can be left unprotected, creating an opportunity for hackers to access confidential information. Insufficient security of APIs is one of the primary sources of cloud data violations. According to Gartner, by 2022, APIs will be the most regularly used vector in cybercrime.
Preventive Measures
- A web application firewall (WAF) can be used to filter incoming requests based on IP address or HTTP header information, as well as to identify code injection attacks. Moreover, WAFs allow for setting quotas for responses for each user or other criteria.
- In order to guarantee the safety of the APIs, it is necessary to implement a range of measures such as tokens, signatures, quotas, encryption, and API gateways into the design of APIs for comprehensive authorization and authentication.
- When selecting an API framework, make sure it has been created with safety considerations in mind. Evaluate the security components and ascertain if it would be secure enough to combine with external applications.
4. Distributed Denial of Service (DDoS) Attacks
Distributed denial-of-service (DDoS) attacks are intended to disrupt a web service, such as a website, by sending numerous requests from numerous sources (therefore, distributed). These requests overwhelm the server, resulting in the inability of the server to respond to legitimate user requests.
Preventive Measures
- Utilize web application scanning tools to conduct a review of your network and system in order to identify any vulnerabilities that may exist.
- When selecting a cloud service, make sure to look for one that provides protection against DDoS attacks. Most platforms do, like AWS Shield, which enables seamless integration with no extra charge.
- Having a backup internet connection in addition to the main one can be beneficial if the primary link is overwhelmed by a high volume of requests. This backup connection should have a separate set of IP addresses.
5. Malicious Insiders
Within any company, insider threats are a major concern in terms of security. These kind of malicious insiders already have permission to access a company’s network and some of the confidential information stored within.
It is particularly hard to identify a malicious insider on the cloud. Companies do not have authority over the basic framework when they use cloud services, making numerous conventional cyber security systems less efficient. On top of that, cloud-based structures are readily accessible from the public web and frequently experience security misconfigurations, making it even tougher to observe malicious insiders.
Preventive Measures
- Ensure that Multi-Factor Authentication is enabled.
- Provide employees with knowledge on how to recognize phishing attempts.
- Utilize automated tools to identify and eliminate phishing emails.
6. Lack of Visibility
When resources are run on infrastructure that a company does not possess, which is the case for cloud-based resources, many classic techniques for achieving network insight are rendered ineffectual. Some businesses that lack security tools specifically intended for cloud usage might have difficulty keeping an eye on their cloud-based resources and defending them from potential threats. This can have a restraining influence on an organization’s capacity to observe their cloud-based resources and keep them secure.
Preventive Measures
- Keep a monitoring and detecting for any dangers.
- Utilizing tools such as a CNAPP will help to reduce the danger and reduce the duration of reaction if an infraction should occur.
Final Words
Moving to the cloud can enable businesses to become more resilient and agile, making them better able to keep up in an unpredictable market. Keep in mind, however, that migrating to the cloud can open up a company to potential security risks if security protocols are not put in place. Do not take the chance of leaving your firm vulnerable – take preventative measures before the problem arises.
