Table of Contents
AWS Shield is a service that is managed by AWS and is used to protect applications from distributed denial of service (DDoS) attacks. It offers detection in real time and automatic mitigation that reduces any downtime or latency for the application, meaning that customers do not have to contact AWS Support to get the protection they need from DDoS.
How AWS Shield works?
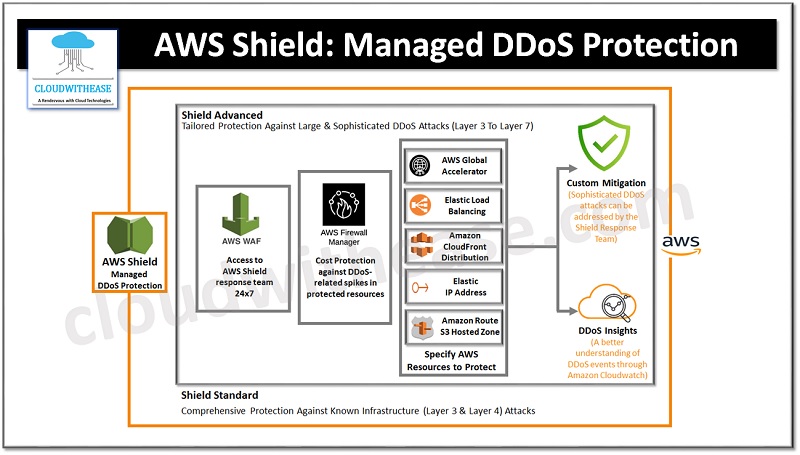
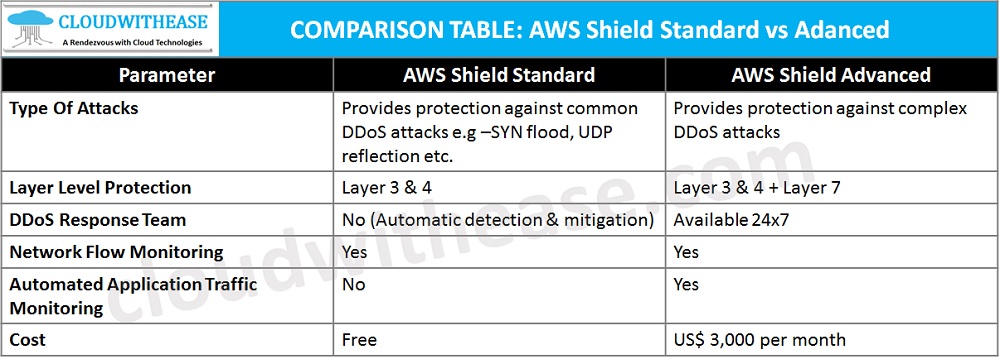
The network and transport levels (layers 3 and 4) as well as the application layer of AWS resources are protected from Distributed Denial of Service (DDoS) attacks by AWS Shield Standard and AWS Shield Advanced (layer 7). Multiple infected systems attempt to overwhelm a target with traffic during a DDoS assault. In addition to blocking genuine end users from using the target services, a DDoS attack might bring down the target owing to an excessive amount of traffic.
AWS Shield offers defense against a variety of well-known and unknown DDoS attack vectors. Shield detection and mitigation is made to offer protection against threats even if they are not immediately known to the service at the time of discovery.
The following are some of the attack types that Shield can identify:
- Network volumetric attacks (layer 3) are a subset of attack vectors for the infrastructure layer. These vectors aim to overwhelm the targeted network or resource’s capacity in an effort to cut off service to authorized users.
- Attacks on network protocols (layer 4) are a subset of infrastructure layer attack vectors. These vectors take use of a protocol to deprive the targeted resource of service. A TCP SYN flood is a typical illustration of a network protocol attack. It can deplete connection state on resources like servers, load balancers, or firewalls. Volumetric attacks on network protocols are also possible. For instance, a bigger TCP SYN flood may aim to deplete the targeted resource or intermediary resources while simultaneously overloading the network’s capacity.
- Attacks on the application layer (layer 7) aim to prevent services from being provided to authorized users by saturating an application with legitimately targeted inquiries, such as web request floods.
AWS Shield Standard: Overview
The perimeter of your application is safeguarded by the managed threat protection solution known as AWS Shield. Application traffic arriving from outside the AWS network first enters at the perimeter.
Think about how people reach your application from the internet when determining the perimeter of your application. Your Amazon Virtual Private Cloud serves as the application boundary if the first point of access is in an AWS Region (VPC). The application perimeter starts at the edge of the AWS network if users are directed to your application by Amazon Route 53 and subsequently access it via Amazon CloudFront or AWS Global Accelerator.
Shield offers DDoS detection and mitigation advantages for all AWS-based applications, but the choices you make when creating your application architecture can affect how resilient your system is to DDoS attacks. DDoS resilience refers to your application’s capacity to function normally despite an assault.
Shield Standard automatically provides protection for all AWS customers at no additional cost. Shield Standard protects your website or apps from the most typical, regularly occurring network and transport layer DDoS attacks. All AWS customers are protected by Shield Standard, but you benefit especially if you use AWS Global Accelerator standard accelerators, Amazon Route 53 hosted zones, or Amazon CloudFront distributions. These resources are completely protected from all recognized network and transport layer threats.
AWS Shield Standard: Benefits
- It is available free of cost.
- The AWS Management Console contains an exclusive dashboard of global threats, where you can access information about DDoS attacks.
- To observe the data that is entering your network and to determine if it is malicious, AWS Shield Standards uses a variety of anomaly algorithms, traffic signatures, and analysis processes.
- When an attack is picked up by AWS Shield Standard, it requires only a fraction of a second to neutralize more than 99% of attacks of infrastructure level.
AWS Shield Advanced: Overview
A managed solution called AWS Shield Advanced can assist you in defending your application from outside threats including DDoS assaults, volumetric bots, and efforts to exploit security flaws. You may get AWS Shield Advanced if you want stronger defenses against assaults.
Shield Advanced offers extended DDoS attack protection for certain resources when you subscribe to it and add protection to them. Your architecture and configuration decisions may have an impact on the safeguards you get from Shield Advanced. Utilize the knowledge in this manual to create and safeguard robust applications using Shield Advanced, and to escalate when professional assistance is required.
AWS Shield Advanced: Benefits
- Make it easier to counteract complicated application-layer attacks (layer 7) by configuring AWS WAF rules which will immediately hinder any malicious traffic.
- The AWS CloudWatch metrics and attack diagnostics offer a way to stay up to date on the current DDoS protection status and get access to real-time reports.
- This shields you from bill hikes due to infrastructure expansion to handle a DDoS attack.
How AWS Shield detects events?
For the AWS network and certain AWS services, AWS has service-level detection tools to guarantee their availability during a DDoS attack. Additionally, resource-level detection algorithms keep an eye on every single AWS resource to make sure that traffic stays within expected bounds. This combination applies mitigations that discard known problematic packets, highlights possibly malicious traffic, and gives priority to traffic from end users, protecting the targeted AWS resource as well as AWS services.
The name of the DDoS attack vector or Volumetric if the evaluation was based on traffic volume rather than a signature will display in your Shield Advanced event summaries, attack details, and Amazon CloudWatch metrics for detected events.
Final Words
When using Amazon EC2, Elastic Load Balancing, CloudFront, and Amazon Route 53, the applications are protected by AWS Shield Standard as a matter of course. If you need more authority and assistance, however, you can opt for the AWS Shield Advanced.
