Table of Contents
What is Azure Virtual Network?
Azure virtual networks or also known as Azure VNETs are the basic building block of your private network on the Azure Cloud. These VNETs are logical constructs which in the underlay utilise the physical infrastructure in Microsoft DCs across different regions thus reaping the benefits i.e., scale, high availability. It is the representation of your private network in Azure that is logically isolated from other VNETs in Azure and is dedicated to your subscription.
Azure Virtual Network Architecture
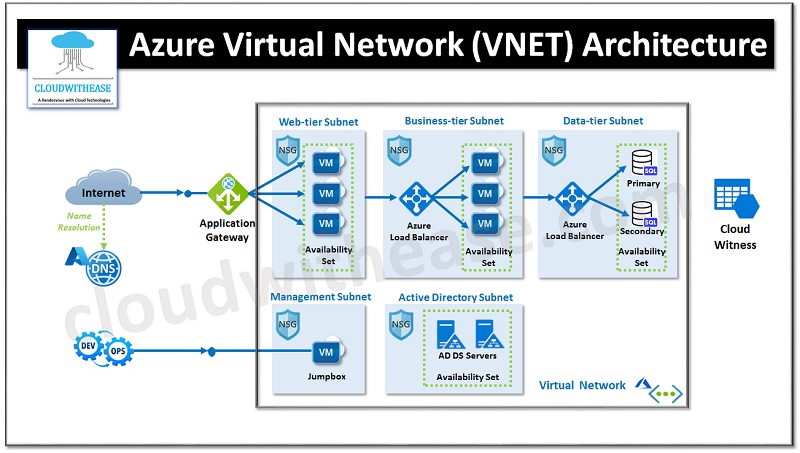
Above diagram depicts a typical n-tier architecture of Azure Virtual Network. The virtual network has been divided into subnets based on the different types of workloads it handles:
- Web-tier Subnet, comprises the user interface.
- Business-tier Subnet, operated business logics.
- Data-tier Subnet, hosts the data source.
It is beneficial to divide Virtual machines into various subnets, as it enables us to apply a different Network Security Group (NSG) to each subnet and thus manage the traffic flow between the tiers.
As an illustration, an HTTP demand from the web should not directly get to the data tier subnet. We can assign an access policy to the Network Security Group of the Subnet linked to the data tier, which only permits incoming requests from the business tier subnet. Any other requests attempting to access the data tier with any protocol apart from the business tier will be declined.
Similarly, we can also assign an access policy on the NSG of the business tier subnet so that the incoming request source IP address falls within the scope of the web tier subnet. Additionally, we can also control the traffic requests to the Active Directory by placing it in a distinct Subnet inside a Virtual Network.
Azure VNET Important Points:
- Each VNET in Azure is assigned a large IP CIDR block range from RFC 1918 address space reserved for private networking.
- 10.0.0.0 – 10.255.255.255 (10/8 prefix)
- 172.16.0.0 – 172.31.255.255 (172.16/12 prefix)
- 192.168.0.0 – 192.168.255.255 (192.168/16 prefix)
- Following address spaces cannot be assigned to a VNET:
- 224.0.0.0/4 (Multicast)
- 255.255.255.255/32 (Broadcast)
- 127.0.0.0/8 (Loopback)
- 169.254.0.0/16 (Link-local)
- 168.63.129.16/32 (Internal DNS)
- You can define multiple Azure VNETs within a single subscription.
- VNETs cannot have overlapping CIDR address ranges.
- Two VNETs cannot by default communicate with each other. In order to allow communication between two VNETs we need to create VNET Peering between VNETs in Azure.
- Resources created within a VNET are assigned private IP addresses automatically from the VNET address range.
- A resource can only be created in a virtual network that exists in the same region and subscription as the resource. You can, however, connect virtual networks that exist in different subscriptions and regions
Subnets:
Once VNET is created, we can create multiple smaller size subnets from this large CIDR range within the VNETs. This allows you to segment your VNET into smaller network spaces.
- A smaller subnet within a VNET must always be from the large IP subnet assigned to VNET in which it is created.
- Subnets within a VNET cannot have overlapping ranges
- For few Azure resources a separate subnet is required, for example Azure VPN gateway is one such resource.
- Azure reserves the first four and last IP addresses for a total of 5 IP addresses within each subnet. Hence, the smallest subnet you can have in Azure is /29 and the largest subnet can be /2.
- Each subnet can be bound to a routing table in which you can add user defined routes for routing traffic to specific destinations i.e., NVAs.
- By default, two subnets within Azure VNETs can communicate with each other.
Network Security Groups:
Network security groups are like traditional ACLs on network devices where we define different permit/deny rules to allow or deny traffic flows.
As we learned the two subnets by default have communication allowed within an Azure Virtual Network, in order to achieve segmentation between the different Azure subnets within a VNET we can use these network security groups to deny communication between subnets in the same VNET.
Azure VNET Communication Types:
- Internet: By default, outbound connectivity to the Internet is enabled for Azure VNET resources. For inbound connections from the internet you either make use of the Public IP address assigned to Azure resources or make use of Azure Load Balancer service.
- On-Premises: You can extend your Azure VNET connectivity to your On-Premises DC via three options as below to enable Hybrid Network Connectivity.
- Point-to-Site VPN Connection
- Site-to-Site VPN Connection
- Azure EXPRESSROUTE
- Connection to Other Azure Resources: You can have different types of communication within Azure as well.
- Resources with a VNET can communicate amongst themselves by default.
- Resources in different VNETs can communicate via VNET peering or via the use of NVAs in VNETs.
Final Words
A virtual network is a group of IP addresses linked together, which is an essential factor to contemplate when devising solutions in the cloud. To ensure that every layer of the application architecture is safeguarded within a reliable network, it is wise to form various subnets for the different levels of the application and attach each subnet to a network security group with limited inbound and outbound rules for security.
