Table of Contents
What is CASB?
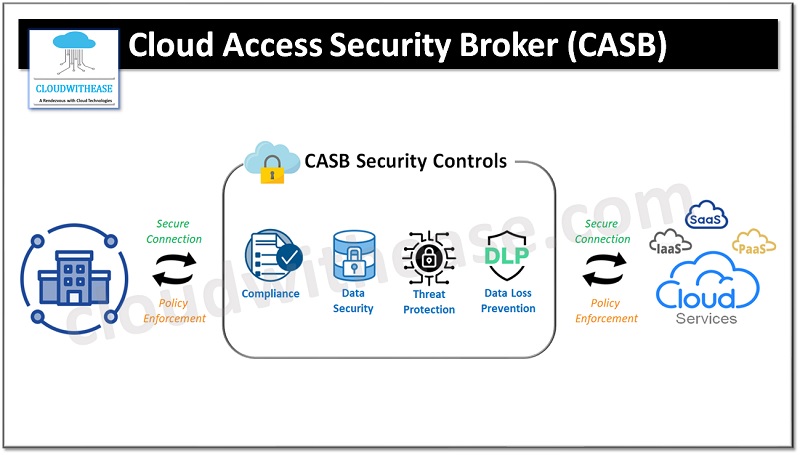
Cloud Access Security Broker, commonly known as CASB, is a crucial component in today’s cloud security landscape. As organizations increasingly adopt cloud services, the need to protect sensitive data stored in the cloud becomes paramount. CASB acts as a gatekeeper, ensuring the security and compliance of data flowing between an organization’s on-premises infrastructure and various cloud services. By providing visibility, control, and threat protection, CASB enables organizations to confidently embrace the benefits of cloud computing while mitigating the associated risks.
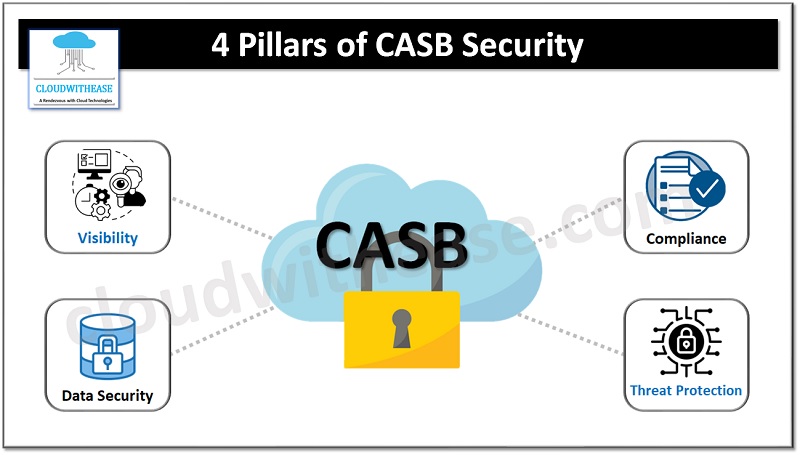
What are the 4 pillars of CASB Security?
CASB security is built on four fundamental pillars: visibility, compliance, data security, and threat protection. These pillars work together to create a comprehensive security framework that safeguards cloud data.
1. Visibility: CASBs offer organizations deep visibility into their cloud environment, providing insights into user activities, data flows, and potential risks. By monitoring and analyzing cloud traffic, CASBs enable organizations to gain a holistic view of their cloud usage and identify any anomalies or vulnerabilities.
2. Compliance: Compliance with industry regulations and internal policies is a critical aspect of cloud security. CASBs help organizations enforce compliance by implementing access controls, data loss prevention measures, and encryption protocols. They also provide auditing and reporting capabilities, ensuring that organizations can demonstrate adherence to regulatory requirements.
3. Data Security: Protecting sensitive data is one of the primary objectives of CASBs. Through data classification, encryption, tokenization, and access controls, CASBs ensure that data stored and transmitted in the cloud remains secure. They also enable organizations to define and enforce data security policies, preventing unauthorized access or data leakage.
4. Threat Protection: CASBs play a vital role in detecting and mitigating cloud-based threats. They employ advanced threat intelligence, anomaly detection, and behavior analysis to identify and block malicious activities. CASBs also integrate with existing security infrastructure, such as firewalls and SIEM solutions, to provide a layered defense approach.
How CASB works to Protect Cloud Data?
CASBs work by intercepting and inspecting traffic between an organization’s network and cloud services. They act as a proxy, allowing them to monitor and control data in real-time. CASBs operate in two primary deployment modes: API-based and proxy-based.
API-based
In an API-based deployment, CASBs integrate directly with cloud service providers’ APIs, allowing them to gain granular visibility and control over cloud applications. This method is non-intrusive and does not require any network configuration changes. CASBs using API-based deployment can monitor activities such as user logins, file uploads, and data sharing, enabling organizations to enforce policies and detect anomalies.
Proxy-based
Proxy-based CASBs, on the other hand, route all network traffic between an organization and cloud services through their gateway. This approach allows CASBs to inspect traffic, apply security policies, and detect threats in real-time. Proxy-based CASBs provide deep visibility into encrypted traffic, ensuring that even SSL-encrypted connections are secure. However, the additional network hop introduced by the proxy can slightly impact performance.
How to Implement a CASB?
Implementing a CASB requires careful planning and consideration of various factors. Here are the key steps to follow when implementing a CASB solution:
1. Assess Your Cloud Environment: Begin by assessing your organization’s cloud environment, including the types of cloud services being used, data storage locations, and user access patterns. This assessment will help you understand the risks and identify the areas where CASB can provide the most value.
2. Define Security Policies: Establish clear security policies that align with your organization’s risk tolerance and compliance requirements. These policies should cover areas such as access control, data protection, and threat detection. Ensure that the policies are enforceable and align with your organization’s existing security infrastructure.
3. Select a CASB Solution: Evaluate different CASB solutions based on their capabilities, integration options, scalability, and support. Consider factors such as deployment models, ease of integration, and compatibility with your existing cloud services. Choose a solution that best meets your organization’s requirements and aligns with your long-term cloud security strategy.
4. Plan the Deployment: Develop a deployment plan that outlines the steps required to integrate the CASB solution into your existing infrastructure. Consider factors such as network configuration changes, user onboarding, and data migration. Ensure that the deployment plan is well-documented and communicated to all stakeholders.
5. Configure and Test: Once the CASB solution is deployed, configure it according to your defined security policies. Test the solution thoroughly to ensure that it is functioning as expected and providing the desired security outcomes. Conduct user awareness training to educate employees about the new security measures and their responsibilities.
6. Monitor and Update: Regularly monitor and analyze the CASB solution to identify any security gaps or emerging threats. Update the solution’s policies and configurations as needed to address new risks or changes in your cloud environment. Stay informed about the latest cloud security trends and best practices to ensure the continued effectiveness of your CASB solution.
Use cases for CASB
CASBs find applications in a wide range of use cases, helping organizations secure their cloud data across various scenarios. Some common use cases for CASBs include:
1. Shadow IT Discovery: CASBs can identify and monitor unauthorized cloud services being used within an organization. By discovering shadow IT, organizations can assess the associated risks and take appropriate actions to secure their data.
2. BYOD Security: CASBs help organizations secure data accessed from personal devices. By enforcing access controls, data encryption, and DLP policies, CASBs ensure that sensitive data remains protected, regardless of the device used.
3. Cloud Application Security: CASBs provide security for cloud applications, including popular SaaS applications like Salesforce, Office 365, and Google Workspace. By applying access controls, data protection measures, and threat detection, CASBs ensure the secure usage of these applications.
4. Compliance and Audit: CASBs play a crucial role in enforcing compliance with industry regulations and internal policies. They provide auditing capabilities, data protection measures, and user behavior analytics, enabling organizations to meet their compliance obligations and pass audits successfully.
5. Cloud Data Protection: CASBs help organizations protect sensitive data stored in the cloud. By implementing encryption, tokenization, and DLP measures, CASBs ensure that data remains secure, even in the event of a data breach.
Choosing the right CASB solution for your organization
Choosing the right CASB solution for your organization requires careful evaluation and consideration of various factors. Here are some key considerations to keep in mind when selecting a CASB solution:
1. Deployment Models: Evaluate the deployment models offered by CASB solutions and choose the one that aligns with your organization’s infrastructure and security requirements. Consider factors such as API-based deployment, proxy-based deployment, and hybrid deployment options.
2. Integration and Compatibility: Assess the integration options and compatibility of CASB solutions with your existing cloud services and security infrastructure. Ensure that the CASB solution can seamlessly integrate with your organization’s cloud environment without disrupting existing workflows.
3. Scalability and Performance: Consider the scalability and performance capabilities of CASB solutions. Evaluate whether the solution can handle your organization’s current cloud usage and scale as your cloud environment expands. Performance considerations should include factors such as latency, throughput, and impact on user experience.
4. Security Capabilities: Assess the security capabilities offered by CASB solutions and evaluate whether they align with your organization’s security requirements. Consider factors such as access control, data protection, threat detection, and compliance enforcement.
5. Ease of Use and Management: Evaluate the user interface and management capabilities of CASB solutions. Consider whether the solution provides an intuitive and user-friendly interface and offers robust management features, such as policy configuration, reporting, and analytics.
6. Vendor Reputation and Support: Consider the reputation and support provided by CASB vendors. Evaluate factors such as vendor experience, customer reviews, and the availability of technical support. Choose a vendor that has a proven track record of delivering reliable and effective CASB solutions.
CASB and SASE
According to a recent report by Gartner, CASBs are seen as a critical component of SASE (Secure Access Service Edge). While CASBs play a vital role in securing cloud usage for companies, they are also an integral part of a broader strategy that businesses should adopt to ensure protection from endpoints to the cloud. In order to achieve comprehensive security, enterprises should also contemplate enhancing CASB capabilities by implementing a secure web gateway (SWG) to safeguard internet usage and a data loss prevention solution (DLP) to protect valuable intellectual property and sensitive corporate data across their network.
Final Words
CASB plays a crucial role in safeguarding cloud data and enabling organizations to embrace the benefits of cloud computing securely. By providing visibility, control, and threat protection, CASBs help organizations ensure the security and compliance of their cloud environment. By choosing the right CASB solution and implementing it effectively, organizations can confidently protect their cloud data and mitigate the risks associated with cloud computing.
