Table of Contents
The rapid growth and adoption of cloud computing has transformed businesses globally but it has also brought numerous security challenges and threats along. The increased utilization of cloud service providers hosting infrastructure involving huge amounts of data is leading to growing concerns around data security and its associated risk of exposure. Human error to cyber attacks could be the cause of data breaches and security attacks.
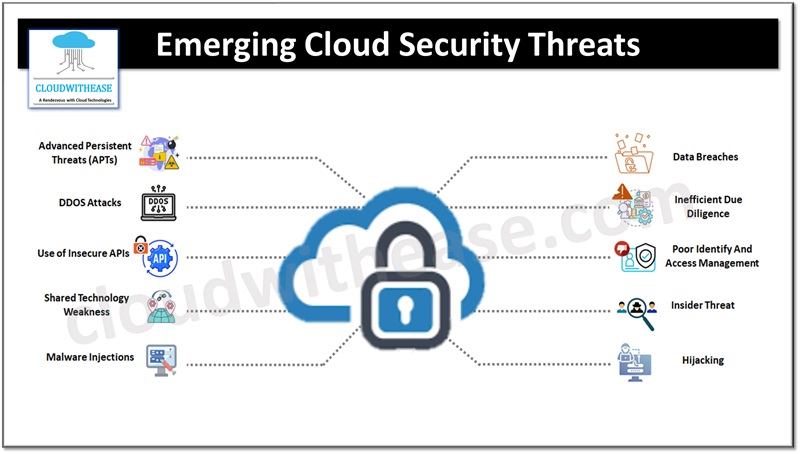
Today we look more in detail about emerging cloud security threats, their impact and how to tackle them effectively to safeguard data and privacy.
Cloud Security Threats Landscape
In spite of being considered secure and well protected cloud systems come with their own risks, challenges, and threats. Let’s look at some most prominent and emerging cloud security risks.
Data Breaches
Data breach involves loss of protected or confidential information to unauthorized personal or groups. This can result with attacks which are targeted in nature or due to poor security practices, application vulnerabilities etc. The data hosted by Cloud Service Providers (CSPs) is numerous and huge which subject them to risk of data breaches. Cloud providers do take the responsibility of their services, but customers and businesses have equal responsibility to protect their own data. Multifactor authentication and encryption techniques are deployed to ensure protection against data breaches.
Weak Identity and Access Management
Attacks and breaches result from absence of multifactor authentication, lack of automated rotation of cryptographic keys and certificates, weak password usage, password sharing, escalated privileges etc. Lack of a robust identity and access management system contribute to unauthorized access to data and systems. OTP and phone authentication based multi factor techniques can help to address such issues. The authentication system should support enforcement of uniform policies on strong password usage, keys rotation etc.
Use of Insecure APIs
Attackers can infiltrate systems and take control, disruption of services , utilization of system vulnerabilities or exploitable code gaps. To ensure security of systems it is required to patch or update systems regularly, perform regular vulnerability scans and follow up on closing vulnerabilities and threats on identified systems.
Hijacking Account or Service
Service hijacking involves phishing, fraud and exploitation of software vulnerabilities which enable attack vectors to misuse account access, data stealing, adversely impacting services and systems in the cloud, and damage the brand reputation.
Insider Threats
Threats emerging due to internal insiders due to human errors or malicious intent are big causes of concern. Service providers need to have robust policies in place, segregation of duties is enforced and logging, auditing, and monitoring of activities performed with privileged accounts is critical to secure the cloud services.
Advanced Persistent Threats (APTs)
Advanced persistent threats steal data and intellectual property by infiltrating organization systems. The common points of entry for an APT could be spear phishing, hacking systems directly or use of insecure third-party networks.
Malware Injection
Malware injection attacks are malicious code and scripts which enable attackers to eavesdrop, steal data, and compromise sensitive information integrity.
Data Loss
Data loss could happen due to multiple reasons such as catastrophe related to human error or nature induced fire or earthquake, or even accidental deletion by the CSP personnel. Providers and users need to ensure robust backup mechanisms are in place and disaster recovery and business continuity strategy is derived, documented, and tested.
Inefficient due Diligence
Performing required due diligence and identifying are business security related requirements before adoption of cloud technology and choosing the right cloud service provider is crucial to have.
Poor IP Protection
Protection of IP requires the highest level and most secure encryption and security protocols. Identification and classification of IP in the proper way is critical to determine potential security risks, vulnerability assessment and controls required to safeguard it.
Cloud Service Abuse
Unsecured cloud service deployments, fraudulent account sign-ups and free cloud services trials could result in large scale automated attacks such as click fraud, hosting of malicious content, DDOS attacks, phishing , email spam etc.
DDOS Attacks
Denial of service or DDOS attacks could lead to large amounts of system resources usage in inappropriate manner such as memory, disk, network bandwidth and processor and cloud result in cloud consumers not able to access cloud resources and applications.
Shared Technology Vulnerabilities
Cloud service providers often use shared infrastructure, applications, and platforms without much alternation to off the shelf hardware and software. If underlying infrastructure components such as CPU cache and GPU do not offer isolation for a multitenant architecture (IaaS), Software as a service (SaaS) and redeployed platforms such as (PaaS) it could lead to shared technology vulnerabilities.
