Table of Contents
Today we look more in detail about IBM Cloud security and compliance center developed in collaboration with IBM research, and its features.
As enterprises are moving onto cloud computing and regulated workloads are also moving onto public clouds. The security and compliance concerns are requiring better management and handling. IBM being a long player in this domain understands the concerns of customers and issues related to various types of client’s requirements.
Today we look more in detail about IBM Cloud security and compliance center developed in collaboration with IBM research, what are its features.
Threat Landscape and Data Breaches
According to an IBM security survey, the cost of data breach continues to rise every year as new attack methods are derived; new vulnerabilities and new risks appear. Average cost of data breaches as per year 2023 was $4.45 million, a 2.3% increase from year 2022 having cost of $4.35 million. As the threat landscape is constantly evolving, businesses find it difficult to secure data and systems if they do not have an effective attack surface management (ASM) and third-party risk management (TPRM) program implemented.
Malware and destructive attacks accounted for 24% and 25% of all cyber-attacks. Cost of damage from a malware attack is estimated at USD $5.13 million. As per the report it takes initially 48 seconds for a threat vector to move laterally within the system.
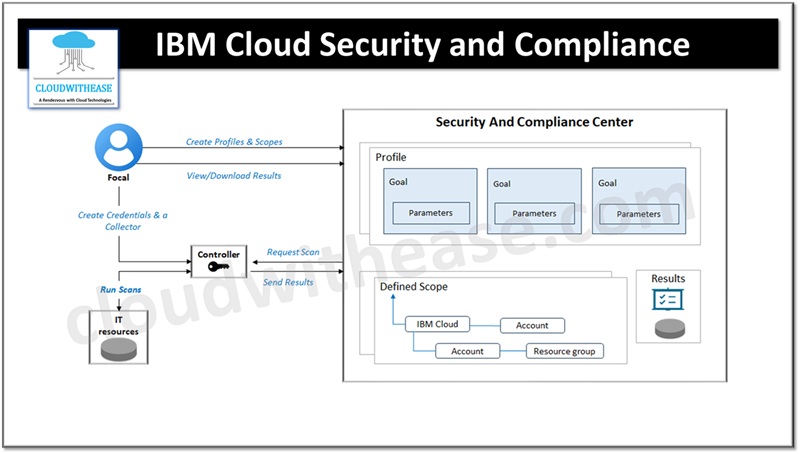
IBM Cloud Security and Compliance
The security and compliance center are integrated into IBM cloud platform. Users can implement controls and continuously assess their security posture and apply rules to enforce standardized configuration for resources hosted in cloud across accounts. IBM also recently acquired Spanugo’s ASAP solution and integrated into IBM Cloud security and compliance center to have hybrid, multi-cloud security and compliance posture for IBM cloud clients.
Create an Instance
To use IBM Cloud and compliance center first create an instance of service.
- Go to IBM cloud catalogue and locate ‘security and compliance center’.
- In the service details page choose location. IBM cloud and compliance center will perform evaluation based on your location.
- Choose a pricing plan. Options include ‘standard’ or ‘Trial’.
- Perform resource configuration by giving name to an instance, specify resource group name and add required tags.
- Acknowledge terms and conditions.
- Click on ‘create’
Assign Access
For large organizations start the assignment process for team members going to manage compliance.
- Create an access group and provide compliance detail
- In console go to Manage🡪 Access (IAM)🡪 Access groups and click to select group to assign access to.
- Click Access 🡪 Assign access
- Assign below permissions by choosing service and review available roles/actions available.
- Services and permissions required
Security and compliance center require minimum permissions of Administrator, Cloud object storage and event notification require reader permissions, Enterprise require administrator or custom role.
Configure Storage
Before starting evaluation of compliance of resources, we need to configure cloud object storage buckets to forward results of data for the purpose of long-term storage.
- To connect to cloud storage bucket open security and compliance center UI and click on settings
- On storage title click connect option
- Prerequisite is to have a service-to-service policy between Cloud Object Storage and Security and Compliance Center is configured.
- Choose an instance of cloud object storage
- From table choose bucket you need to use and click on connect
Scan Resources
- In security and compliance UI go to attachments page and click create.
- Provide a name and description to the attachment.
- Choose profile and profile version which you wish to use for evaluation.
- Customize the evaluations in scan while editing default parameters to match specific use cases.
- Click Next and set the frequency for evaluation of resources such as every day, 7 days, every 30 days and so on.
Scan is scheduled when an attachment is created and post scan completion, results are available in IBM security and compliance dashboard.
