CEH
$4.99
CEH Interview Q&A Vol 1.0
Description
CEH Interview Q&A Vol 1.0
Questions 50
Check the complete list of questions:
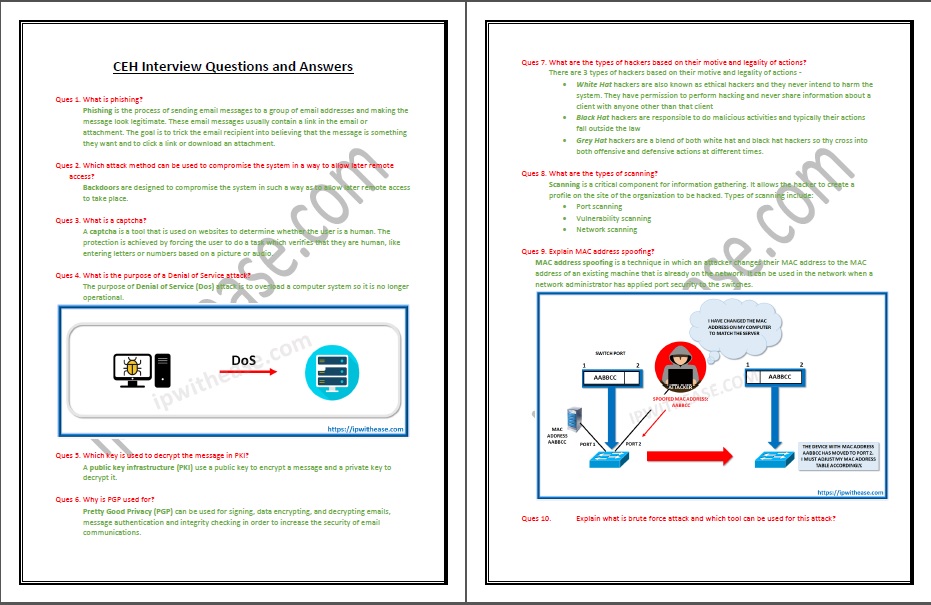
- What is phishing?
- Which attack method can be used to compromise the system in a way to allow later remote access?
- What is a captcha?
- What is the purpose of a Denial of Service attack?
- Which key is used to decrypt the message in PKI?
- Why is PGP used for?
- What are the types of hackers based on their motive and legality of actions?
- What are the types of scanning?
- Explain MAC address spoofing?
- Explain what is brute force attack and which tool can be used for this attack?
- What is the most common form of DoS attack?
- How you can prevent against Cross Site Request Forgery (CSRF) attack?
- What is IPsec and why is it used for?
- How to avoid Man-in-the-middle attacks?
- Define ransomware and explain countermeasure for protection?
- According to OWASP top 10 security risks what is the most dangerous web vulnerability?
- What is footprinting?
- What is a sniffing attack?
- What is the difference between passive and active reconnaissance?
- What is enumeration?
- What is the difference between asymmetric and symmetric encryption?
- What is a firewall?
- What is the difference between worm and virus?
- What is Keylogger and Keylogger Trojan?
- What is NULL Scan?
- Explain Black box testing?
- What is TCP SYN message in three-way handshake?
- What is Open-source intelligence (OSINT)?
- What is Maltego?
- What is Snort?
- What is the difference between hashing and encryption?
- Explain cyber kill chain process?
- Explain DNS spoofing?
- What is hash collision attack in cryptography?
- What are WPA and WPA2?
- What is Kismet?
- Write OpenSSL command that will check TLS/SSL of website named test.com openssl s_client -connect www.test.com:443
- Explain buffer overflow?
- How many antivirus programs should be installed on a single system at the same time?
- User wants to send secret message by hiding it within jpeg image. What technique is used in this scenario?
- Hacker sends a legitimate looking email message asking users to update their information on the company’s website. URL in the email point to a false website. What technique is used in this scenario?
- Assume that website testwebsite.com may contain sensitive information about username and passwords in pdf files. What query input will help you to search that files using Google as a search engine?
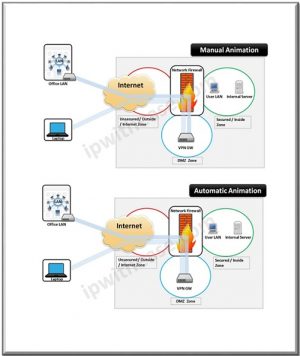
- What is the purpose of a DMZ on a network?
- User with computer IP address 10.10.10.10 fails to access web server at IP address 10.10.10.100. You decide to run wireshark in client computer to check if the messages are going to the web server. What wireshark filter will show the connections from the client computer to web server?
- Administrator needs to permit http traffic in the host 10.100.0.2 and UDP traffic in the host 10.100.0.3. He also needs to permit all HTTPS traffic to the rest of the network and deny all other traffic. What should be changed in following configuration in order to achieve this?
- Explain SQL injection attack and which method can be used to reduce the risk of falling victim to a SQL injection attack?
- A network administrator realized that some users are connecting their notebooks in the wired network to have Internet access. What should be done in order to prevent unauthorized access to wired network?
- Which nmap scan does not completely open a TCP connection?
- Explain nmap -T0 option and when you would use it?
- Write nmap command that will execute http and https port scan for all hosts that belong network 10.2.3.0/24 except host 10.2.3.20?


Reviews
There are no reviews yet.