Cisco FTD
₹442.29
Cisco FTD Interview Q&A Vol 1.0
Description
Cisco FTD Interview Q&A Vol 1.0
Questions 52
Check the complete list of questions:
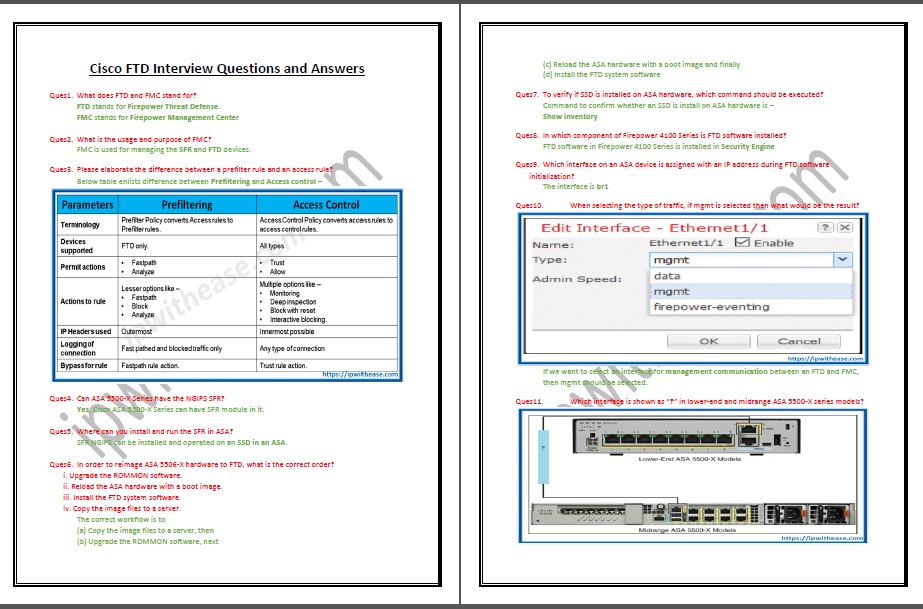
- What does FTD and FMC stand for?
- What is the usage and purpose of FMC?
- Please elaborate the difference between a prefilter rule and an access rule?
- Can ASA 5500-X Series have the NGIPS SFR?
- Where can you install and run the SFR in ASA?
- In order to reimage ASA 5506-X hardware to FTD, what is the correct order
- To verify if SSD is installed on ASA hardware, which command should be executed?
- In which component of Firepower 4100 Series is FTD software installed?
- Which interface on an ASA device is assigned with an IP address during FTD software initialization?
- When selecting the type of traffic, if mgmt is selected then what would be the result?
- Which interface is shown as “?” in lower-end and midrange ASA 5500-X series models?
- What is the name of the Mgmt interface which CLI shows, when connected to Firepower Code and when connected to ASA code?
- Which command is used in FTD to view the statistics of events inside the encrypted tunnel between FTD and the FMC?
- Which command confirms whether FTD is registered with the FMC?
- Which command is used to configure a manager in an FTD?
- What are the capabilities of the Firepower in terms of Licenses?
- Describe the usage and functionality of Base and Threat Licenses?
- Describe the usage and functionality of Malware and URL Filtering licenses?
- If we go to the System > Licenses > Smart Licenses page, we see Evaluation Mode button. What is the time period of the evaluation mode?
- What happens when we turn on the Evaluation Mode on the Firepower System?
- What is the workflow to Purchase, Generate, and Apply a Smart License in Firepower System?
- What is the behaviour of FTD when it is deployed in a Routed Mode?
- If you want to install FTD Version 6.1 on Firepower 9300 appliance having FXOS Release 1.1.4, what is the correct order of action?
- Which file can be deployed directly into an ESXi host if we are installing/running FMC?
- Which command syntax would be correct, if we want to ping test from FTD to the FMC?
- Which port does the Firepower System use for management communication by default?
- If we hit enter in the highlighted prompt, what would be the default firewall mode?
- In below snippet, when registration with the manager is completed, the IP 10.1.1.16 is of which device?
- Which command is used to configure FTD from Transparent Mode to Routed Mode?
- What is the behaviour of FTD when it is deployed in a Transparent Mode?
- In what mode firewall is configured in below snippet?In what scenario do Gig interfaces and BVI interface have same IP?
- Which command provides an overview of the various components of an inline interface set?
- What is the first-level-defense mechanism implemented on Firepower Engine?
- Which directory stores the filed related to DNS Policy?
- Which licenses are necessary to block a URL based on its category and reputation?
- Which type of analysis requires a connection to the cloud?
- Which base policy enables the largest number of standard text Snort rules by default?
- Which NAT section has highest priority during rule evaluation?
- After you deploy a new NAT policy, if a connection still uses a rule from the prior version of the NAT policy, how could you ensure that FTD will use the new policy?
- What is Security Intelligence?
- What is the function of Network Analysis Policy?
- What is the function of Intrusion Policy?
- What is Access Control Rule Monitor Action?
- What is Access Control Rule Trust Action? What is Access Control Rule Blocking Actions?
- What is Access Control Rule Interactive Blocking Actions?
- What is the function of Network Discovery Policies? What are 2 types of Network Discovery mechanisms?
- What is the purpose of Firepower Recommended Rules?
- How many connectivity models are there for network analysis and intrusion policies in Firepower System?
- Describe Balanced Security and Connectivity network analysis and intrusion policies?
- Describe Maximum Detection network analysis and intrusion policies?
- Describe No Rules Active intrusion policy?



Reviews
There are no reviews yet.